🎧 Listen to this article
Narrated by Talon · The Noble House
In January 2025, hackers breached Gravy Analytics and leaked a business model, not a bug.
Gravy Analytics was one of the largest location data brokers in the world. The breach exposed millions of precise GPS coordinates harvested from over a thousand popular mobile apps: Flightradar24, dating apps, transit trackers, games. The company was collecting location data not through code embedded in apps, but through the real-time bidding process of digital advertising.
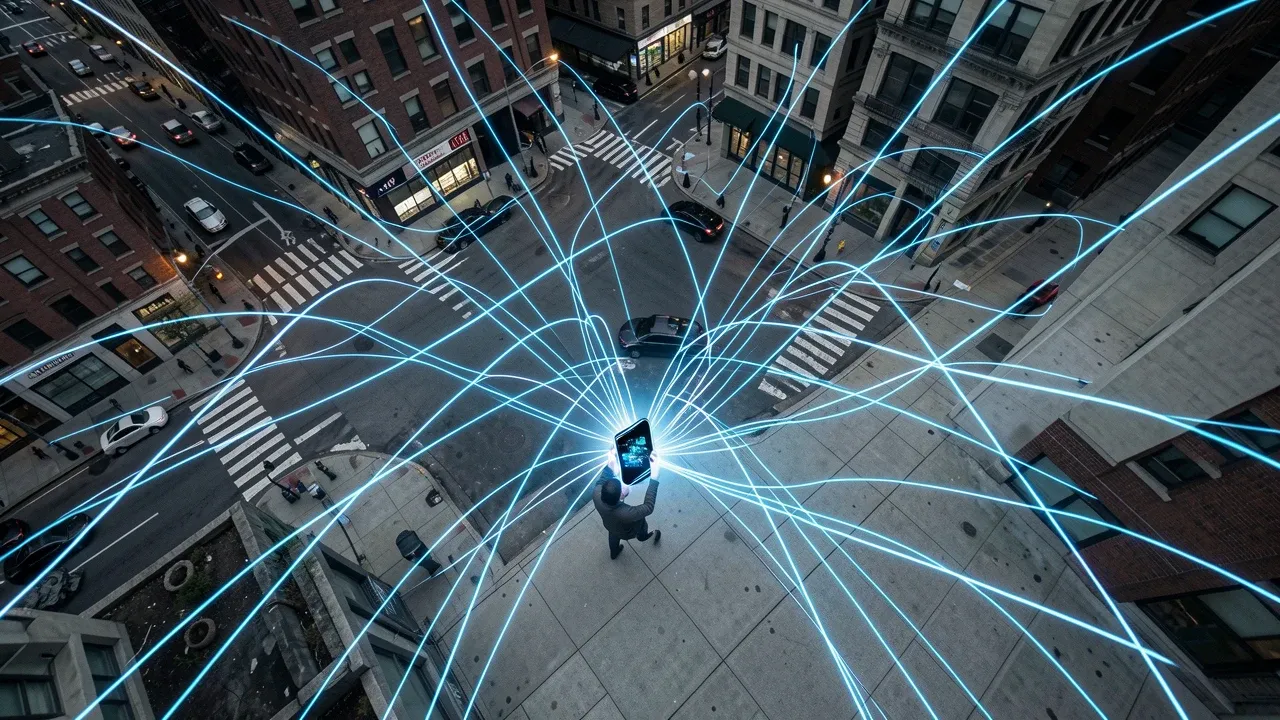
Every time an ad loaded on your phone, your precise location was broadcast to dozens of companies in milliseconds. Gravy Analytics was listening to that broadcast, collecting the coordinates, and selling them — to commercial clients, to government contractors, and through its subsidiary Venntel, to federal law enforcement including ICE and the IRS.
The app on your phone that watches everything is not one app. It's the advertising infrastructure underneath all of them.
The FTC had already been investigating before the breach
In December 2024, the FTC announced a proposed order against Gravy Analytics and Venntel for "unlawfully tracking and selling sensitive location data." The order, finalized in early 2025, prohibited the companies from selling location data tied to sensitive sites, including healthcare facilities, places of worship, domestic violence shelters, and schools, and required deletion of all historically collected data.
The FTC's complaint laid out the mechanics without ambiguity. Gravy Analytics collected location data from approximately one billion mobile devices per day (FTC enforcement action, Jan 2025). The data was precise enough to track individuals to specific buildings. It was sold in bulk, with no meaningful consent from the people being tracked. Most users of the apps feeding data to Gravy had no idea it was happening because the data collection occurred at the advertising SDK level, not through app permissions they had consciously granted.
Then the breach happened. Forbes reported on January 10, 2025, that the leaked data could identify individuals who visited LGBTQ+ venues, military installations, abortion clinics, and addiction treatment centers. The data was not anonymized in any meaningful sense. A sequence of GPS coordinates over time is a fingerprint. Show me where a phone sleeps at night and where it goes at 9 a.m., and I'll tell you who owns it.
How your phone bleeds data without your knowledge
The average smartphone user has between 40 and 80 apps installed. A 2025 analysis by PrivacyHawk found that the typical user's data is held by over 300 companies, most of which the user has never heard of and never consciously shared data with.
The pipeline works like this. You install an app. The app includes an advertising SDK from Google AdMob, Meta Audience Network, or one of dozens of smaller ad networks. When the app loads an ad, the SDK broadcasts a bid request to an ad exchange. That request includes your device's advertising ID, your IP address, your precise GPS coordinates if location permissions are granted, your device model, your operating system version, and sometimes your age and gender. This bid request is sent to hundreds of potential advertisers in real time. Most don't win the bid. But all of them receive the data.
Data brokers like Gravy Analytics positioned themselves as participants in the bidding process specifically to harvest this data stream. They never intended to buy ads. They were there to collect coordinates. The result is a shadow surveillance network that operates entirely within the legal framework of digital advertising. No warrant needed. No court order required. The data is "consented to" through a privacy policy that no human has ever read.
The regulation is real but riddled with gaps
The Protecting Americans' Data from Foreign Adversaries Act, signed in 2024, prohibits data brokers from selling personally identifiable sensitive data to foreign adversary countries, specifically China, Russia, Iran, and North Korea. In February 2026, the FTC sent warning letters to multiple data brokers reminding them of their PADFAA obligations, with penalties of up to $53,088 per violation (FTC press release, Feb 2026).
But PADFAA has a glaring gap: it only restricts sales to foreign adversaries. Selling the same data to domestic companies, to U.S. law enforcement without a warrant, or to political campaigns remains legal in most states. The FTC's Gravy Analytics order was a case-specific enforcement action, not a general rule. There is no federal privacy law that comprehensively regulates how data brokers collect, aggregate, and sell location data from mobile devices.
At the state level, the picture is fragmented. California's Delete Act, signed October 2023, created a mechanism for consumers to request deletion of their data from all registered brokers through a single portal. Texas sued Meta in 2024 for collecting biometric data without consent. Most states have nothing. Mondaq's January 2026 legal analysis predicted the FTC's first enforcement action under PADFAA could come in 2026, noting the agency had identified data brokers offering sensitive data to entities connected to foreign adversary countries.

The permission prompt on your phone is a misleading question
When your phone asks "Allow this app to access your location?", you think you're granting access to the app. In practice, you're granting access to every company in the app's advertising supply chain, a chain that can include dozens of intermediaries, each with their own data retention policies, their own customers, and their own security vulnerabilities.
Apple's App Tracking Transparency framework, introduced in iOS 14.5 in 2021, gave users the ability to deny cross-app tracking. Roughly 75 percent of users opted out. But ATT only blocks Apple's advertising identifier. It does not prevent apps from collecting GPS coordinates, IP addresses, or device fingerprints, all of which can be used for tracking. Google's Privacy Sandbox for Android, still rolling out through 2025 and 2026, aims to replace third-party cookies and advertising IDs with privacy-preserving alternatives. The real-time bidding infrastructure that enabled the Gravy Analytics model remains fundamentally intact.
What you can actually do about it
The honest answer is: less than you'd like. You can deny location permissions to apps that don't need them. You can use "While Using" instead of "Always" for apps that do. You can disable your advertising ID entirely — both iOS and Android now allow this. You can use a VPN to mask your IP address. You can periodically review which apps have which permissions.
But you cannot opt out of the real-time bidding ecosystem without opting out of ad-supported apps entirely. And you cannot know which of the hundreds of companies receiving your bid-request data will be breached next.
The surveillance isn't a feature of any single app. It's the business model of the entire advertising ecosystem, and the only thing standing between your location history and a public database is the security practices of companies you've never heard of.
Sources
Sources: FTC enforcement action against Gravy Analytics and Venntel, finalized Jan 2025 · Forbes, Gravy Analytics breach report (Jan 10, 2025) · FTC, PADFAA warning letters (Feb 2026) · Mondaq, Privacy Law Recap 2025 (Jan 27, 2026) · PrivacyHawk, data broker analysis (2025) · California Delete Act, signed Oct 2023 · Apple, App Tracking Transparency (iOS 14.5, 2021)


